On April 1, 2021, San Francisco-based technology company CodeCov discovered that attackers had compromised its software platform, which over 29,000 customers use worldwide to test software code. While that was troubling enough, the tampering reportedly started back in January, and it may have continued undetected had it not been for some astute observations made by a customer. The attacker exploited a container design mistake and exported credentials from a Docker image, allowing the attacker to modify the upload script and exfiltrate sensitive information.
The CoveCov incident highlights the importance of software supply chain security in the modern tech industry. In this blog post, we will discuss why software supply chain attacks have become increasingly common in recent years, how they work, and how to protect your organization from them.
What is the software supply chain?
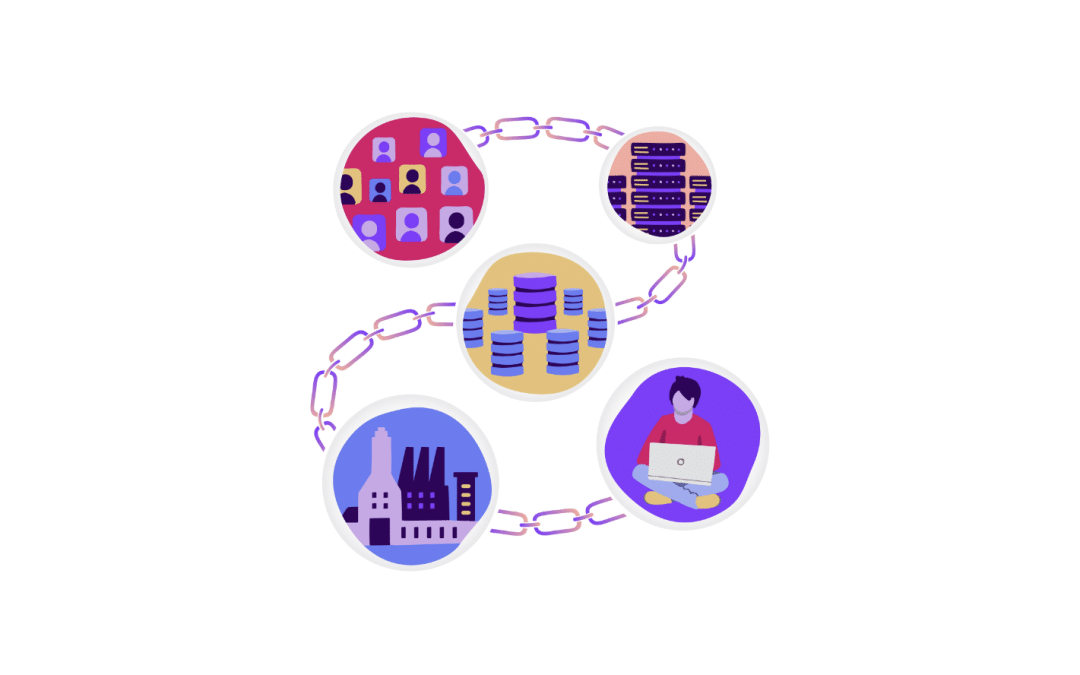
So what exactly is the software supply chain? Simply put, it’s the process that connects different nodes in the software development cycle, from idea conception to deployment. First, it involves turning an idea or a problem into code, which is then pushed out to a place where people can download it as an application. Next, feedback from customers is incorporated into the development cycle, and the process starts all over again.
The software supply chain is more conceptual than the physical supply chain, but the principles are similar. Just as physical products are made up of smaller components and assembled in a factory, software is made up of different pieces of code and built into an application.
Increased risk with automation
However, unlike the physical supply chain, the software supply chain is highly automated and spreads across various development tools, often SaaS or cloud-based. Companies no longer store their code in private repositories inside their internal network but instead use public services like GitHub or BitBucket. Automation drives the software pipeline and monitors the code as it flows through it, gets tested, and is pushed into production.
But with all this automation comes increased risk. Sensitive information is vulnerable to exploitation at every step of the software supply chain, and source code recently became a lucrative target for malicious actors. It can be encrypted for ransom or used as a jumping-off point to infiltrate other organizations.
What is a software supply chain attack?
Software supply chain attacks can infiltrate the supply chain at any point to compromise the code or steal sensitive information. The attacker then uses the obtained information for lateral movement or launching further attacks. So how does a supply chain attack affect business?
The SolarWinds attack is a prime example of a software supply chain attack. In this supply chain attack, a Russian nation-state hacker infiltrated an update server connected to the internet and changed the code of an update being pushed. This update included a remote access Trojan that was automatically installed, and Windows Defender was disabled. The attackers then hid behind the legitimate activity performed by SolarWinds and gained access to internal information of the directly impacted clients and all their affiliated contractors. This attack affected many organizations, including private companies like Intel and public organizations like the Department of Defense and the Pentagon.
Protecting against software supply chain attacks
So, what can organizations do to protect themselves against software supply chain attacks?
Implement a software bill of materials
One approach to avoid supply chain attacks is to implementing a software bill of materials (SBoM). An SBoM is a list of all the different applications and open-source libraries used inside the pipeline, which can help with version control and ensure that vulnerabilities are minimized. By having a clear understanding of the software components that make up their applications, organizations can better track any security vulnerabilities that may exist and ensure that they are patched in a timely manner.
Conduct thorough security audits
Another approach to prevent supply chain attacks is ensuring that all software components are thoroughly vetted for security vulnerabilities before being added to the supply chain. This means conducting security audits on third-party software and open-source libraries, as well as maintaining up-to-date security patches and software updates. Organizations must also limit access to their software supply chain, using a zero-trust security model, to ensure that only authorized personnel can make changes to the code.
Implement the principle of least privilege
An important way to protect against software supply chain attacks is by implementing the principle of least privilege (PoLP). This principle involves granting users and applications the minimum level of access required to complete their tasks. In software development, this means restricting access to sensitive parts of the software supply chain, such as code repositories and build servers, to only those who need it. By limiting the number of people who can access the software supply chain components, organizations can reduce the likelihood of unauthorized access and minimize the impact of any potential breaches. Additionally, implementing PoLP can also help organizations identify potential insider threats by monitoring user activity and enforcing access controls. By combining PoLP with other security measures, such as software audits and zero-trust architectures, organizations can build a strong defense against software supply chain attacks.
Maintain up-to-date security patches
Maintaining up-to-date security patches is an essential step in protecting against software supply chain attacks. New vulnerabilities are discovered all the time, and software companies release patches to fix them as quickly as possible. Organizations must stay on top of these patches and ensure that all software components in their supply chain are up to date with the latest security fixes. This includes not only third-party software but also internally developed software. Failure to keep software up to date can leave organizations vulnerable to known exploits that attackers can easily leverage. Automated patch management systems can help organizations keep their software components up to date and reduce the risk of supply chain attacks. Additionally, organizations must have a process in place to respond quickly to newly discovered vulnerabilities and apply patches in a timely manner.
Prioritize security throughout the software development lifecycle
It’s worth noting that software supply chain attacks are not limited to third-party software components. Even internally developed software can be vulnerable to attacks if proper security measures are not in place. As such, organizations must prioritize security throughout the software development lifecycle, from conception to deployment, to minimize the risk of supply chain attacks.
Conclusion
In conclusion, software supply chain attacks are a growing threat to organizations of all sizes, and it’s critical to take steps to secure the software supply chain. Implementing a software bill of materials, conducting thorough security audits, maintaining up-to-date security patches, and using a zero-trust security model can all help organizations protect themselves against these types of attacks. By prioritizing security throughout the software development lifecycle, organizations can minimize the risk of supply chain attacks and protect their sensitive information from exploitation by attackers.
How can Zilla Security help?
Zilla Security helps organizations combat software supply chain attacks by using the principle of least privilege and conducting regular and thorough security audits.
Zilla makes it easy to achieve and maintain a strong security posture with automated user access reviews and tracking of access rights for all your users. In addition to the comprehensive reports, you get an extensive library of out-of-the-box integrations with code repositories and deployment tools, such as GitHub and BitBucket, Jenkins, and many more. You also have access to our expert resources for understanding complex access rights in any cloud or SaaS application.
To learn more about software supply chain’s security, compliance, and audit readiness with Zilla Security, contact us